Blog Body
Renad Almajed Group (RMG) is the first consulting company to successfully implement the CYBER SECURITY
Renad Almajed Group (RMG) is the first Saudi consulting company that succeeded in implementing the SAMA Cyber Security Framework application project as it implemented it in the Saudi Home Loans (SHL) because of the importance and necessity of this framework to achieve the requirements of the current digital community that has high expectations with experience Flawless customers, constant availability of services and effective protection of sensitive data. The origins of information and online services are now of strategic importance for all public and private institutions, as well as for the wider community.
These services are vital to creating a vibrant digital economy. It has also become systematically important to the economy and broader national security. All this confirms the need to protect sensitive data and transactions, and thus ensure confidence in the Saudi financial sector in general.
Therefore, we find that the Saudi Arabian Monetary Agency (SAMA) is now imposing the adoption of the application of this framework on all (“member organizations”) operating in the field of loans, banks, financial services and insurance in order to identify and effectively address risks related to cyber security to maintain the protection of information assets and services via the Internet.
What is cyber security?
Cyber security is defined as a set of tools, policies, security concepts, security guarantees, guidelines, risk management approaches, procedures, training, best practices, safeguards, and technologies that can be used to protect an organization’s information assets from internal and external threats.
General security objectives include:
- Confidentiality – the information assets can only be accessed for persons authorized to access (i.e. protected from unauthorized disclosure or (cancellation) the intended leakage of sensitive data).
- Integrity – the information assets are accurate and complete and properly processed (i.e. protected from unauthorized modification, which may include authenticity and non-repudiation).
- Availability – information assets are flexible and accessible when required (i.e. protected from unauthorized outages).
Therefore, we find that the framework defines the principles and objectives for initiating, implementing, maintaining, monitoring and improving cyber security controls in member organizations. The framework provides cyber security controls that apply to the organization’s information assets, including:
- Electronic information.
- Physical information.
- Applications, programs, electronic services and databases.
- Computers and electronic devices (such as ATMs).
- Information storage devices (for example, hard disk, flash drive).
- Buildings, equipment and communication networks (technical infrastructure).
The framework has a correlation with other institutional policies in related areas, such as physical security and fraud management.
Applicability
Where does cyber security apply?
The framework applies to all member organizations organized by the Saudi Arabian Monetary Agency, which include the following:
- All banks operating in the Kingdom of Saudi Arabia.
- All insurance and/or reinsurance companies operating in the Kingdom of Saudi Arabia.
- All finance companies operating in the Kingdom of Saudi Arabia.
- All credit offices operating in the Kingdom of Saudi Arabia.
- Financial market infrastructure
The most important features of cyber security
- Responsibilities
The framework is mandated by the Saudi Arabian Monetary Agency. The monetary agency is the owner and is responsible for the periodic updating of the tire.
Member organizations are responsible for adopting and implementing the framework.
- Explanation
The Saudi Arabian Monetary Agency SAMA, as the framework owner, is solely responsible for providing interpretations of principles, objectives, and control considerations, if necessary.
- The target audience
The framework aims to senior and executive management, business owners, owners of information assets and those responsible for participating in defining, implementing and reviewing cyber security controls within member organizations.
- Audit update and maintenance
The Saudi Arabian Monetary Agency will periodically review the framework to determine the effectiveness of the framework, including the effectiveness of the framework to counter emerging cyber security threats and risks. If possible, the Saudi Arabian Monetary Agency will update the framework based on the audit findings.
If a member organization considers that updating the framework is required, it must provide the required update formally to the Saudi Arabian Monetary Agency. The Saudi Arabian Monetary Agency will review the requested update, and upon approval, the framework will be modified
The frame structure has its advantages
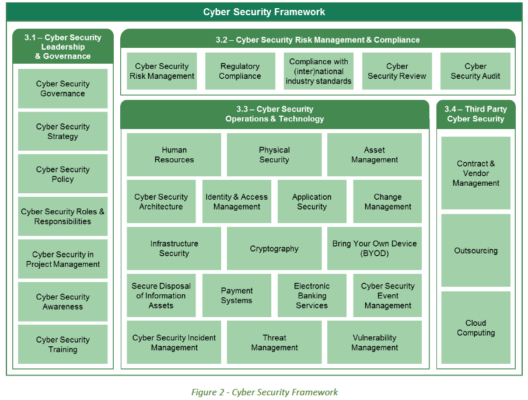
The framework is structured around four main domains, namely
- Cyber Security Leadership and Governance.
- Cyber security risk management and compliance
- Cyber security operations and technology.
- 3rd party cyber security.
For each domain several subdomains are defined. The subdomain focuses on a specific topic of cyber security. For each subdomain, the framework provides for initial, objective and monitoring considerations
The principle summarizes the main set of required cyber security controls related to subdomain.
The target describes the purpose of the principle and what the required set of cyber security controls are expected to achieve.
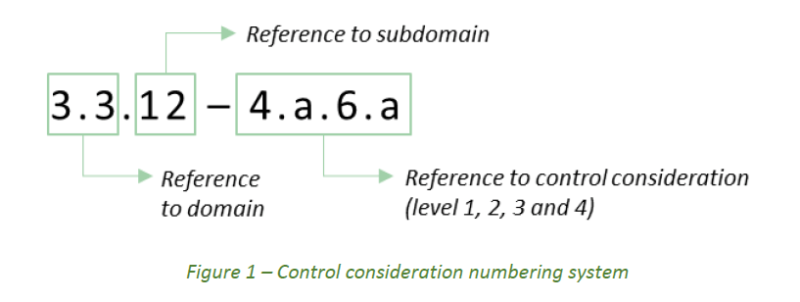
Monitoring considerations reflect mandatory cyber security controls that must be taken into account. Control considerations are uniquely numbered throughout the tire. Where appropriate, consideration of control can consist of up to 4 levels.
Control considerations are numbered according to the following numbering system:
The figure below shows the general structure of the framework and indicates cyber security and sub-domains, including reference to the applicable section of the framework.
Self-evaluation, review and audit
Self-evaluation, review, and audit
Implementation of the framework in the organization will be subject to periodic self-evaluation. The organization will conduct a self-assessment based on a questionnaire. The Saudi Arabian Monetary Agency will review and review self-assessments to determine the level of compliance with the framework and the maturity level of cyber security in the organization.
Cyber Security Maturity Model
The level of cyber security maturity will be measured with the help of a predefined cyber security maturity model. The cyber security maturity model characterizes 6 maturity levels (0, 1, 2, 3, 4, 5), summarized in the table below. In order to achieve levels 3, 4 or 5, the organization must first meet all the criteria for previous maturity levels.
| Explanation | Definition and Criteria | Maturity Level |
| Cyber security controls are not in place. There may be no awareness of the particular risk area or no current plans to implement such cyber security controls. |
* No documentation. *There is No awareness or attention for certain cyber security control. |
0 Non-existent |
| *Cyber security control design and execution varies by department or owner. *Cyber security control design may only partially mitigate the identified risk and execution may be inconsistent. |
*Cyber security controls are not or partially defined. * Cyber security controls are performed in an inconsistent way. * Cyber security controls are not fully defined. |
1 Ad-hoc |
| *Repeatable cyber security controls are in place. However, the control objectives and design are not formally defined or approved. * There is limited consideration for a structured review or testing of a control. |
*The execution of the cyber security control is * based on an informal and unwritten, though standardized, practice. |
2 Repeatable but informa |
| *Cyber security policies, standards and procedures are established. * Compliance with cyber security documentation i.e., policies, standards and procedures is monitored, preferably using a governance, risk and compliance tool (GRC). * key performance indicators are defined, monitored and reported to evaluate the implementation. |
*Cyber security controls are defined, approved and implemented in a structured and formalized way. * The implementation of cyber security controls can be demonstrated. |
3 ctured and formalized |
| Effectiveness of cyber security controls are measured and periodically evaluated. *key risk indicators and trend reporting are used to determine the effectiveness of the cyber security controls. * Results of measurement and evaluation are used to identify opportunities for improvement of the cyber security controls. |
*The effectiveness of the cyber security controls are periodically assessed and improved when necessary. * This periodic measurement, evaluations and opportunities for improvement are documented. |
4 Managed and measurable |
| *The enterprise-wide cyber security program focuses on continuous compliance, effectiveness and improvement of the cyber security controls. * Cyber security controls are integrated with enterprise risk management framework and practices. * Performance of cyber security controls are evaluated using peer and sector data. |
*Cyber security controls are subject to a continuous improvement plan. | 5 Adaptive |
The objective of the framework is to create an effective approach to addressing cyber security and managing cyber security risks within the financial sector. To achieve an appropriate level of cyber security maturity, member organizations must operate at least at the maturity level 3 or higher as shown below.
Third Maturity Level (3)
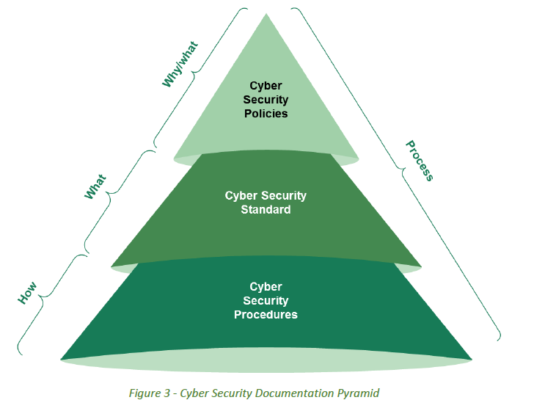
Cyber security documents must clearly indicate “why”, “what” and “how” cyber security controls should be implemented. Cyber security documents consist of cyber security policies, cyber security standards and cyber security measures.
Cyber security policy must be adopted and delegated by the organization’s council and clarify “why” cyber security is important to the organization. The policy should highlight the origins of the information that must be protected and “what” are the principles and goals of cyber security that must be developed
Based on cyber security policy, cyber security standards must be developed. These “what” standards define what cyber security controls must be implemented, such as security and system standards, separation of duties, password rules, event monitoring and backup and recovery rules. Standards support and enhance cyber security policy and should be considered as baselines of cyber security.
Step-by-step tasks and activities that staff, third parties, or WHO clients should perform in cyber security procedures are detailed. These procedures define “how” cyber security controls, tasks and activities should be implemented in the operating environment and support the protection of the organization’s information assets in accordance with cyber security policy and standards.
The process is defined in the context of this framework as an organized set of activities designed to achieve the specified goal. The process may include policies, standards, guidelines, procedures, activities and work instructions, as well as any of the roles, responsibilities, tools and management controls required to reliably deliver outputs.
Actual progress in the implementation, performance, and compliance of cyber security controls should be monitored and evaluated periodically using Key Performance Indicators (KPIs).
Fourth Maturity Level (4)
To achieve the fourth level of maturity, the organization must periodically measure and evaluate the effectiveness of implemented cyber security controls. In order to measure and assess whether cyber security controls are effective, key risk indicators (KRI) must be identified. The KRI indicates an effectiveness measurement criterion and must determine whether the actual outcome of the measurement is less than or is working on or above the target base. KRIs are used to report trends and identify potential improvements.
Fifth Maturity Level (5)
The fifth level of maturity focuses on the continuous improvement of cyber security controls. Continuous improvement is achieved through continuous analysis of the goals and achievements of cyber security and the identification of structural improvements. Cyber security controls must integrate with enterprise risk management practices and be supported by real-time automated monitoring.
Business process owners should be responsible for monitoring compliance with cyber security controls, measuring the effectiveness of cyber security controls, and incorporating cyber security controls within the enterprise risk management framework. Additionally, the performance of cyber security controls must be evaluated using peer and segment data.
We are pleased to serve you by filling in the contact form