Blog Body
Find out in detail what the tasks of the National Cyber Security Authority in the Kingdom, its role in enhancing digital security, and how you can achieve compliance with the Authority’s controls in cooperation with experts from Renad Al-Majd Company (RMG).
In light of the rapid digital transformation that the Kingdom of Saudi Arabia is witnessing to achieve the goals of Vision 2030, cyberspace has become a vital arena that requires superior protection and advanced defense strategies. Cybersecurity is no longer just a technical option, but has become an urgent national necessity to protect the vital interests of the state, its technical assets, and sensitive infrastructure.
Hence, the pivotal role of the National Cybersecurity Authority (NCA) as a policy-setting body, standards, and controls has emerged. Many leaders in the public and private sectors are wondering about the precise roles of this entity, and the fact is that regulating and setting controls in the sector is one of the main tasks of the National Cyber Security Authority, but it is not the only one. In this article, we will dive deep into the competencies and responsibilities of the Authority, and how organizations can align their work with these requirements to ensure a safe and reliable work environment.
Strategic organization and national policy development
When talking about the tasks of the National Cybersecurity Authority, the legislative and regulatory role comes to the forefront. The Authority is the national reference in the Kingdom for cybersecurity affairs, and this includes building a comprehensive governance system.
- Preparation of the National Cybersecurity Strategy
The Authority is working to formulate and update the National Cybersecurity Strategy and supervise its implementation. This strategy aims to create a secure and reliable Saudi cyberspace that enables growth and prosperity. This requires high-level coordination with all government and private entities to ensure the integration of efforts and unify visions.
- Issuance of Guidelines and Controls
Security cannot be achieved without clear standards. Therefore, the issuance of Cybersecurity Core Controls (ECC) and Cybersecurity Controls for Sensitive Systems (CSCC) is an integral and essential component of the National Cyber Security Authority‘ s mandate.This mission includes:
- Remote Work Controls: To ensure the security of information outside of the workplace.
- Cybersecurity controls for cloud computing: To regulate the relationship between service providers and beneficiaries.
- Frameworks: such as the Open Source Framework and others.
Protecting Critical Infrastructure and Interests
The Authority’s responsibilities go beyond the theoretical and legislative aspects to reach the practical and defensive aspects. Protecting the country’s sensitive infrastructure is one of the most sensitive and important tasks of the National Cyber Security Authority, as this includes the financial, health, energy, telecommunications, and sovereign government sectors.
Incident Monitoring and Response
DEWA has a National Cyber Operations Center, which operates around the clock to monitor threats. Through this center, the following is done:
- Attack Monitoring: Detecting malicious cyber attempts targeting national entities.
- Early Warning: Issuing proactive alerts to the affected or targeted parties to take the necessary actions.
- Emergency Response: Providing support and assistance to entities in the event of serious cyber incidents, ensuring that the damage is contained and service is restored as quickly as possible.
Promote compliance and effective oversight
The Authority does not only set laws, but also monitors their implementation. Following up on the compliance of entities with the issued controls and policies is a key pillar of the National Cyber Security Authority (NCSA) to ensure that the Saudi digital space is free of loopholes.
Verification and evaluation mechanisms
The Authority conducts periodic assessments of the security situation of national entities. This includes:
- Measuring the extent of the entities’ commitment to the application of the Basic Controls (ECC).
- Conduct vulnerability assessments in government systems and networks.
- Issue compliance reports that outline the strengths and weaknesses of entities, helping decision-makers improve their security posture.
Licensing and Regulation of the Cybersecurity Market
To ensure the quality of services provided in this sensitive sector, the Authority has assumed the responsibility of regulating the market. The issuance of licenses to cybersecurity service providers is an important activity that falls within and is classified as one of the tasks of the National Cyber Security Authority.
This mission aims to:
- Ensure that cybersecurity service providers are qualified and possess the necessary competencies.
- Protecting beneficiaries of substandard services.
- Stimulating investment in the local cybersecurity sector and supporting national startups in this field.
National Capacity Building and Awareness
The human element is the strongest and weakest link in the cybersecurity system. Recognizing this, the Authority has made building national capacities and spreading community and institutional awareness an integral part of the tasks of the National Cyber Security Authority.
Training and Educational Initiatives
- Cyber Exercises: Organizing attack simulation exercises to train the competent teams in government agencies on response mechanisms.
- Scholarship and Training Programs: Qualifying young national cadres to bridge the gap in the labor market.
- Raising awareness: Launching awareness campaigns targeting all segments of society to introduce cyber risks and ways to protect against them (such as awareness campaigns against phishing and electronic fraud).
International Cooperation and Representation of the Kingdom
Cyber threats do not recognize geographical boundaries. Therefore, representing the Kingdom in relevant regional and international organizations, bodies, and committees is one of the strategic tasks of the National Cyber Security Authority. The Authority works to:
- Establishing partnerships and agreements with developed countries in this field to exchange experiences and information.
- Participate in the formulation of international cybersecurity standards.
- Enhancing the Kingdom’s position in global cybersecurity indicators, and the Kingdom has achieved qualitative leaps in this regard thanks to the efforts of the Authority.
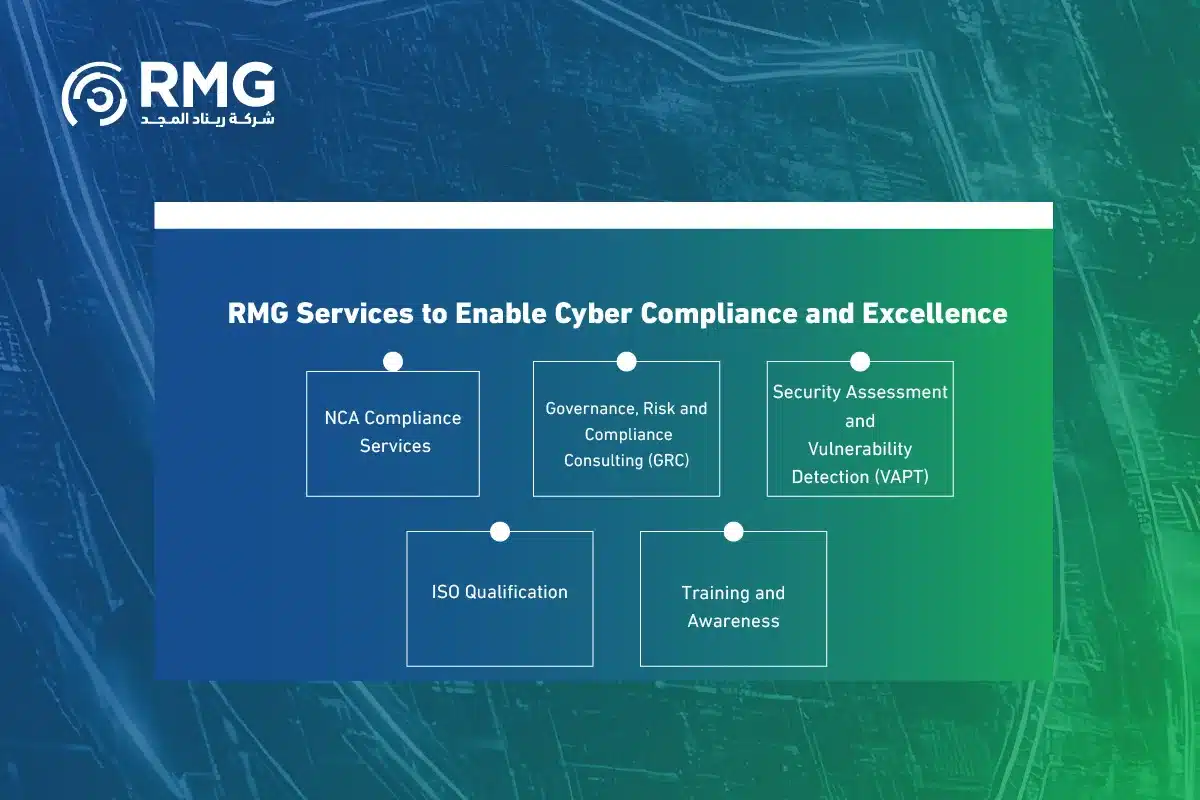
RMG Services to Enable Cyber Compliance and Excellence
After our detailed review of what falls under the mandate of the National Cyber Security Authority, it becomes clear how much responsibility falls on government entities and companies to achieve compliance and protect their assets. This is where Renad Al Majd (RMG) comes into play as a leading strategic partner in the Kingdom, providing a full package of services that ensure that you not only comply with the Authority’s requirements, but also reach the highest levels of cyber maturity.
Our services are comprehensive and professional, and include:
- NCA Compliance Services :
- Qualifying entities to apply the basic controls for cybersecurity (ECC-1:2018).
- Qualifying Entities for Cybersecurity Controls for Sensitive Systems (CSCC-1:2019).
- Apply Data Cybersecurity Controls (DCC).
- Remote Work Controls (TCC) and Cloud Computing Controls (CCC) compliance services.
- Governance, Risk and Compliance (GRC) Consulting:
- Building cybersecurity strategies aligned with the organization’s goals and requirements.
- Developing security policies and procedures.
- Cyber risk management in accordance with international standards (ISO 27005).
- Security Assessment and Vulnerability Detection (VAPT):
- Perform penetration tests for networks, web and mobile applications.
- Assess vulnerabilities and provide detailed reports on remediation plans.
- ISO Qualification:
- Equipping facilities to obtain ISO 27001 (Information Security Management System) certification.
- ISO 22301 (Business Continuity) certification.
- Training and Awareness:
- Implementing awareness programs for employees to raise the sense of security.
- Simulate phishing attacks to measure employee awareness.
Call to Collaboration: Fortify Your Foundation with Renad Al-Majd
Achieving cybersecurity requirements is no longer a luxury, but an investment in the sustainability of your business and protecting your organization’s reputation. Being aware of the tasks of the National Cyber Security Authority is the first step, and the second step is choosing the ideal implementation partner.
We invite all government entities, private sector companies, and vital institutions to contact Renad Al-Majd Company (RMG). Our expert advisors are ready to provide an initial consultation session, in which we discuss your current security posture and draw a clear roadmap towards full compliance and sustainable digital security.
Don’t wait for the cyber incident to happen.. be proactive and choose Renad Al-Majd as a partner for your success and security.
Frequently Asked Questions about the Tasks of the National Cyber Security Authority
We conclude our article by answering the most frequently asked questions on the topic, to provide a quick reference for the reader:
1. Is issuing violations and penalties considered one of the tasks of the National Cyber Security Authority?
Yes, the Authority has the authority to monitor and verify the compliance of the entities with its controls, and in case of non-compliance, the Authority submits its reports to the competent authorities, and has mechanisms to ensure the application of the standards, which enhances the mandatory force of its controls.
2. What is the difference between ECC and CSCC?
The ECC is binding on all government and private sector entities that have sensitive national infrastructure, while the CSCC has higher security requirements for systems classified as “very sensitive” within those entities.
3. Does DEWA provide direct technical solutions to entities (e.g. protection programs)?
The role of the Authority is primarily regulatory, supervisory, and legislative. The provision of technical solutions and the purchase of software is the responsibility of the entity itself, but these solutions must be in accordance with the standards set by the Authority, which is what Renad Al-Majd consultants help you with.
4. How does the Authority contribute to the protection of employees within the entities?
By obliging entities to develop security policies, and enforce awareness and training programs, which makes the digital work environment safer for employees and protects them from falling victim to cyber attacks.
5. Is regulating the cybersecurity market considered one of the tasks of the National Cyber Security Authority?
The Authority is responsible for licensing cybersecurity service providers in the Kingdom to ensure the quality and reliability of the services provided to national and sensitive entities.